Explore the Platform
Live UIs are available when the management cluster is running. Screenshots shown as fallback.
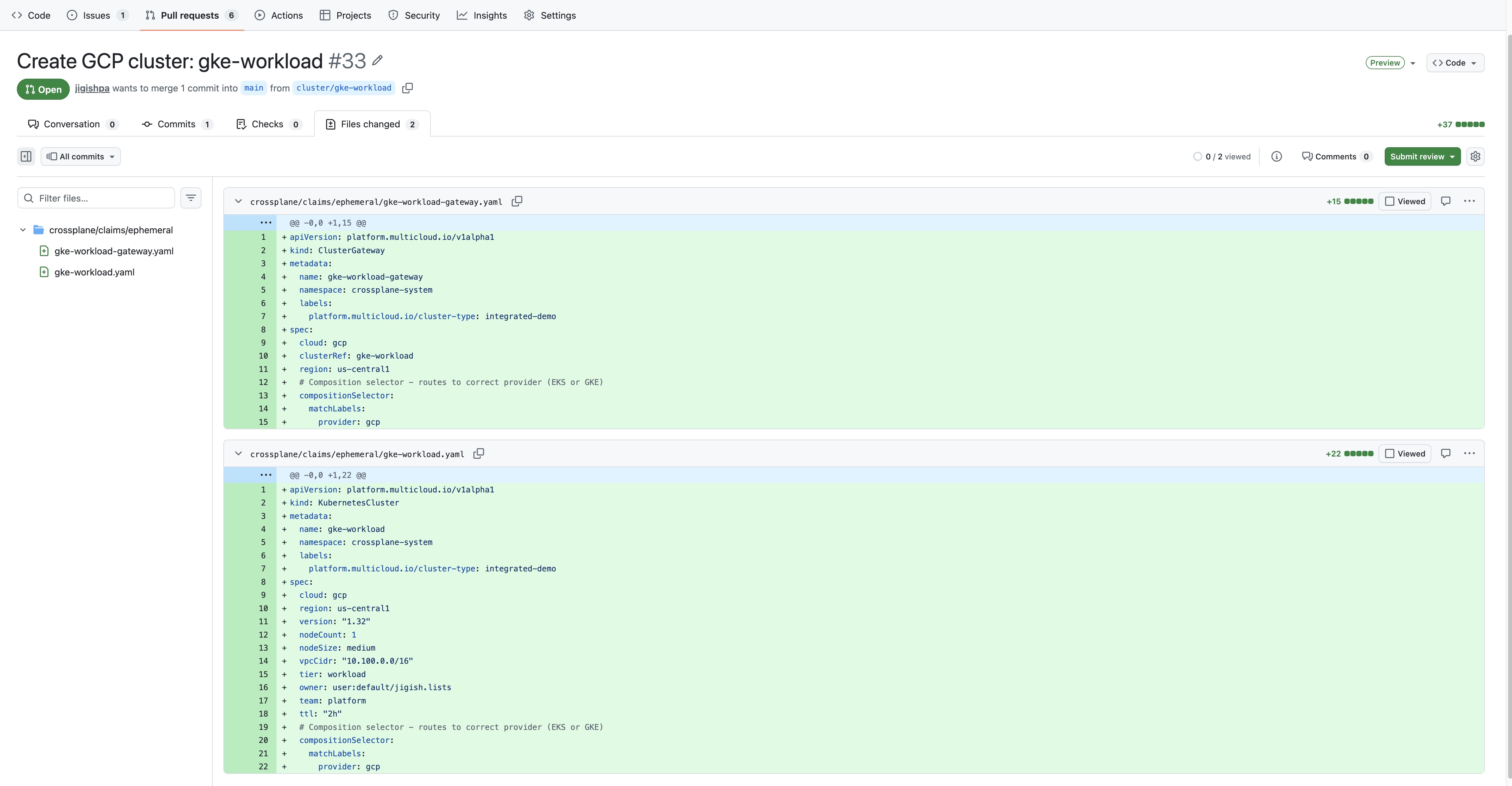
ArgoCD
GitOps continuous delivery. App-of-apps pattern managing 30+ applications across clusters.
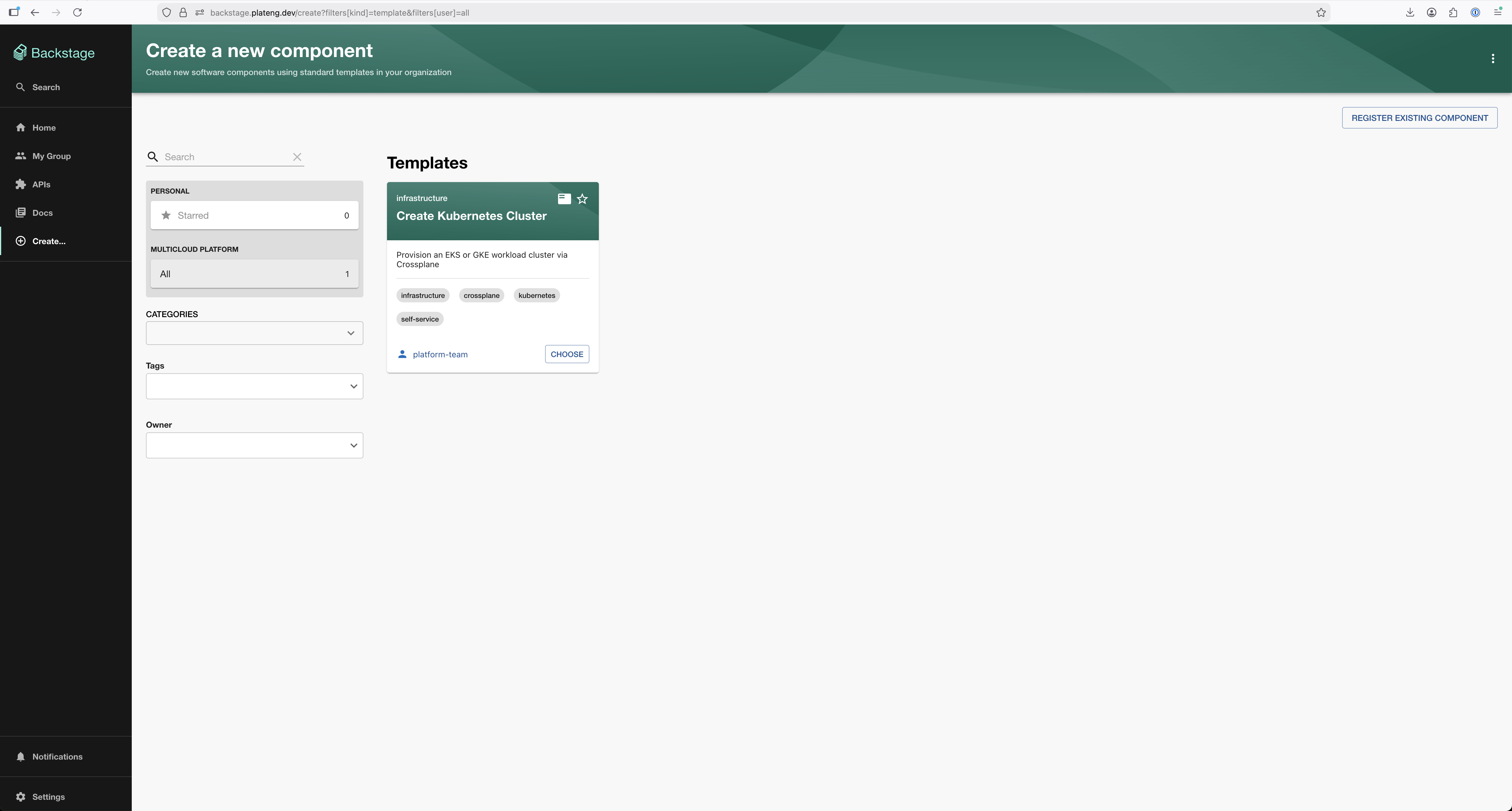
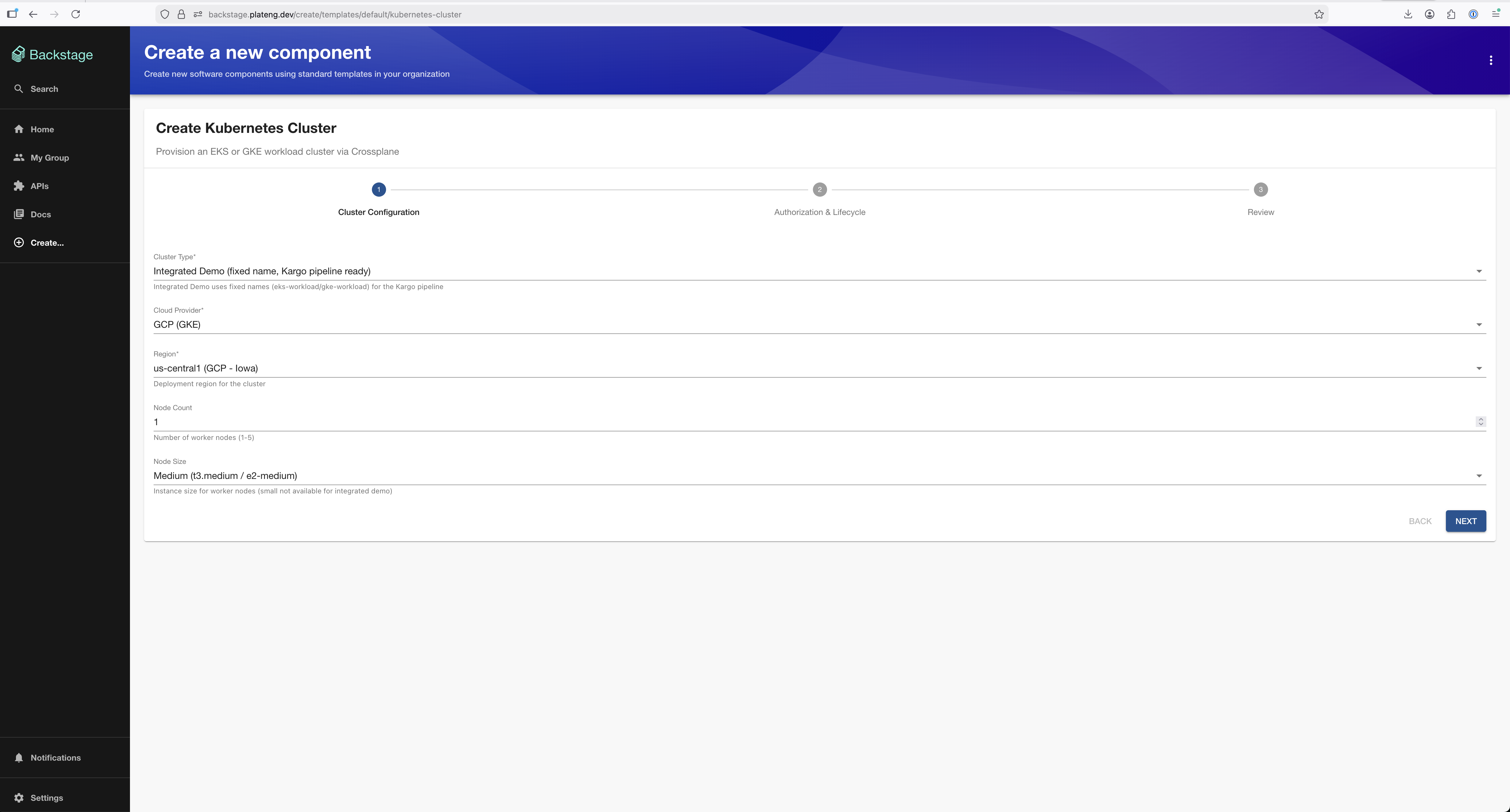
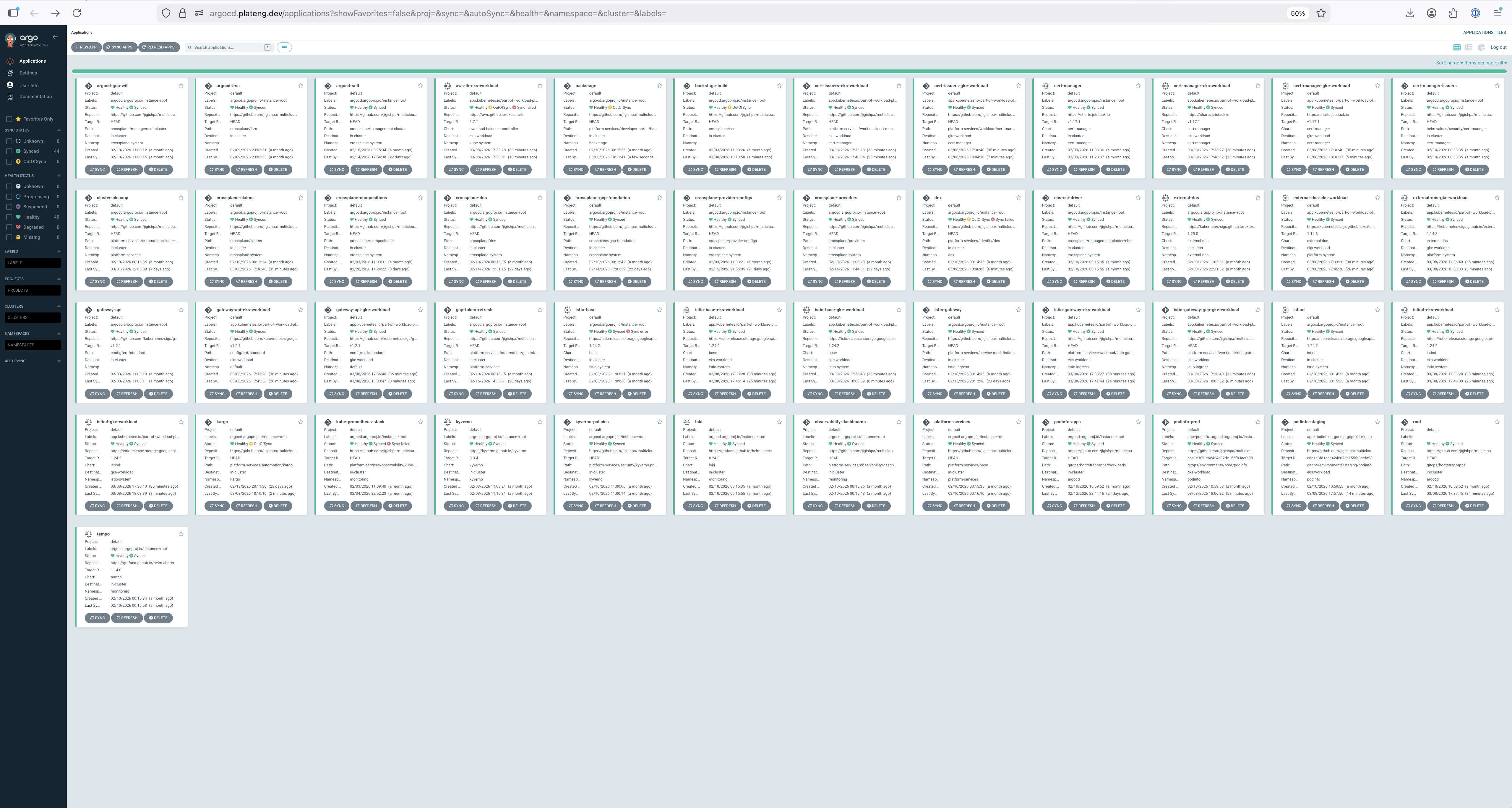
Backstage
Developer portal with software catalog, cluster creation templates, and TechDocs.

Grafana
Full LGTM observability stack — Prometheus metrics, Loki logs, Tempo traces.
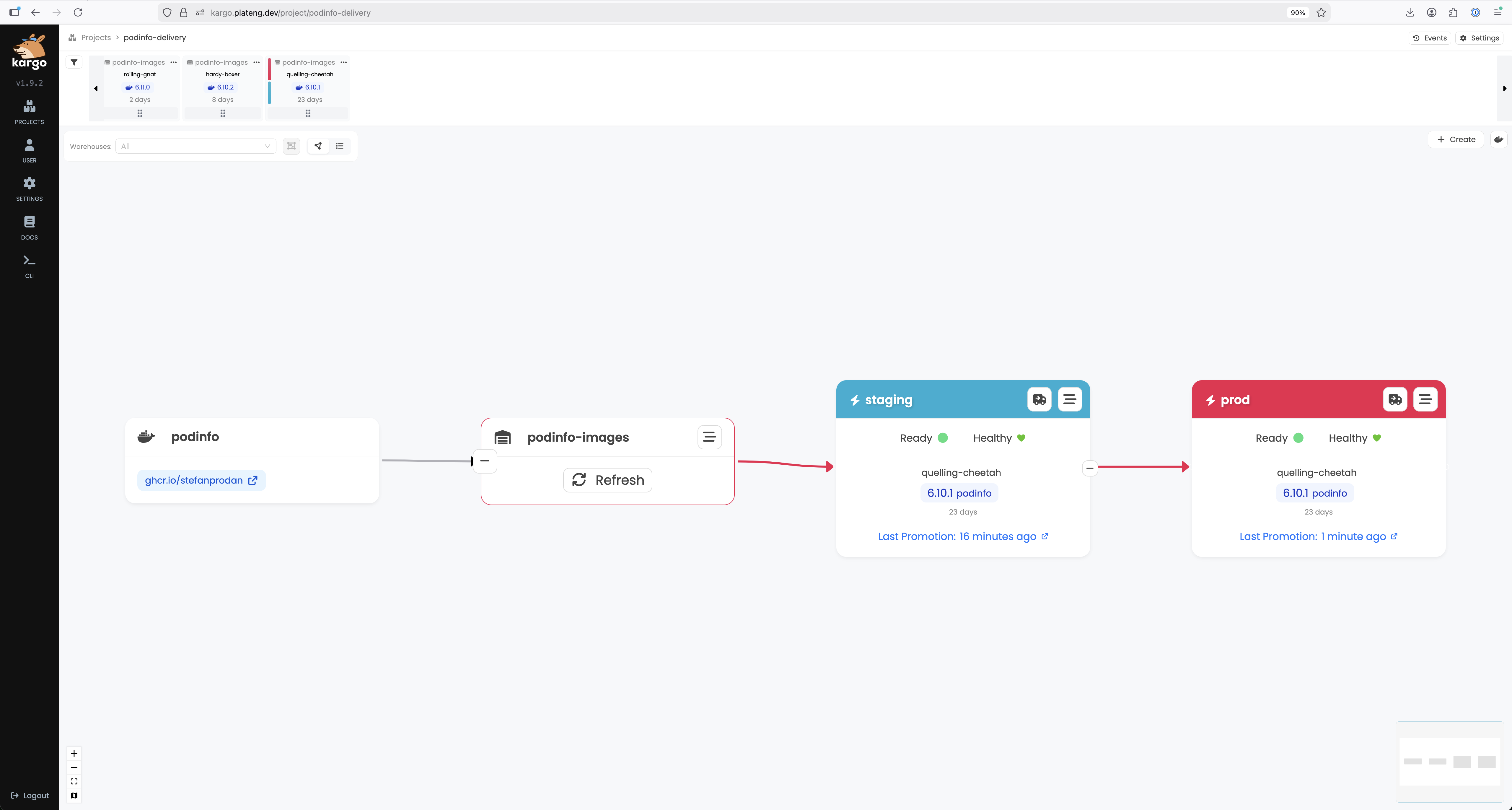
Kargo
GitOps-native progressive delivery. Promotion pipelines from staging to production.
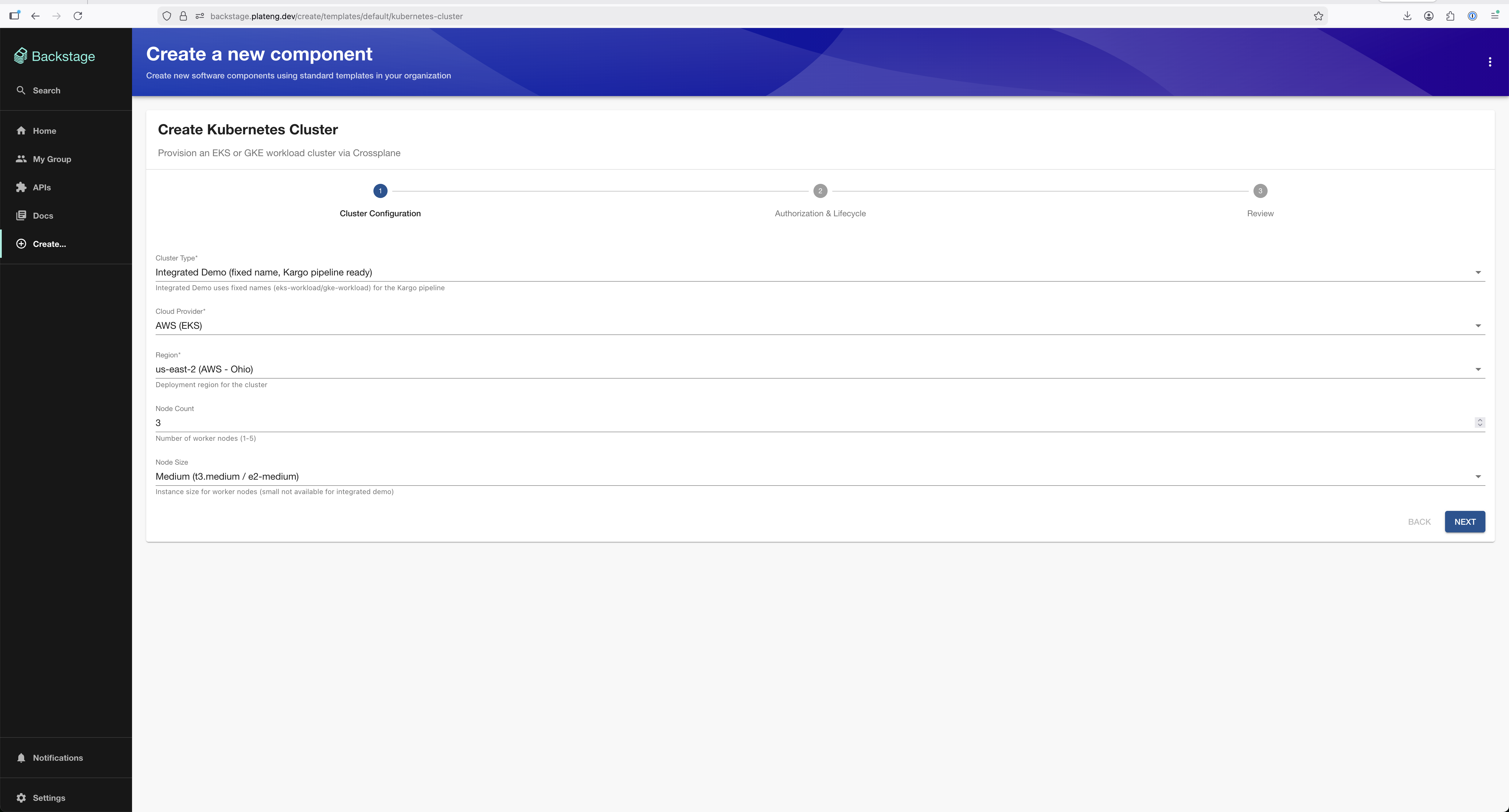
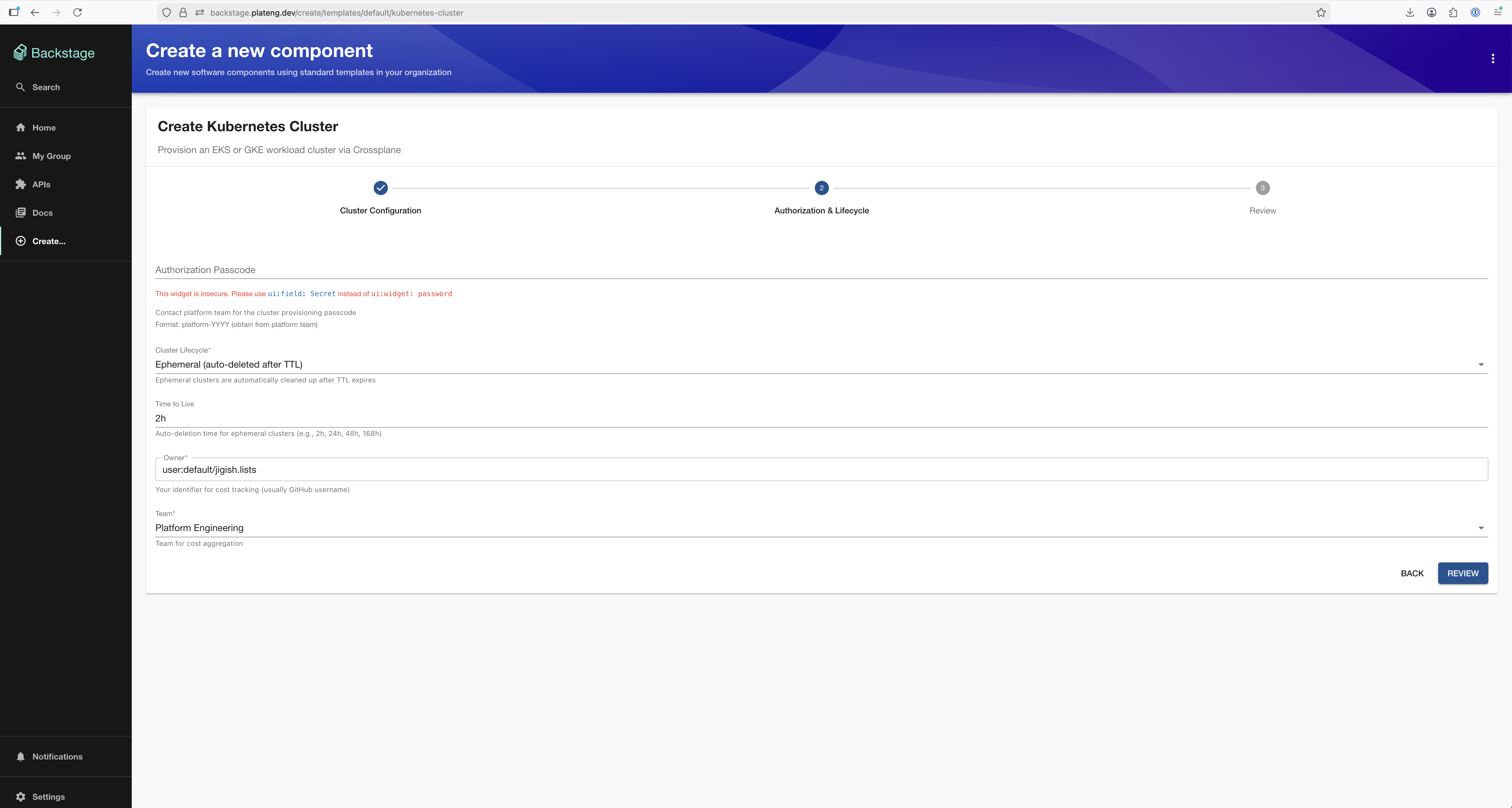
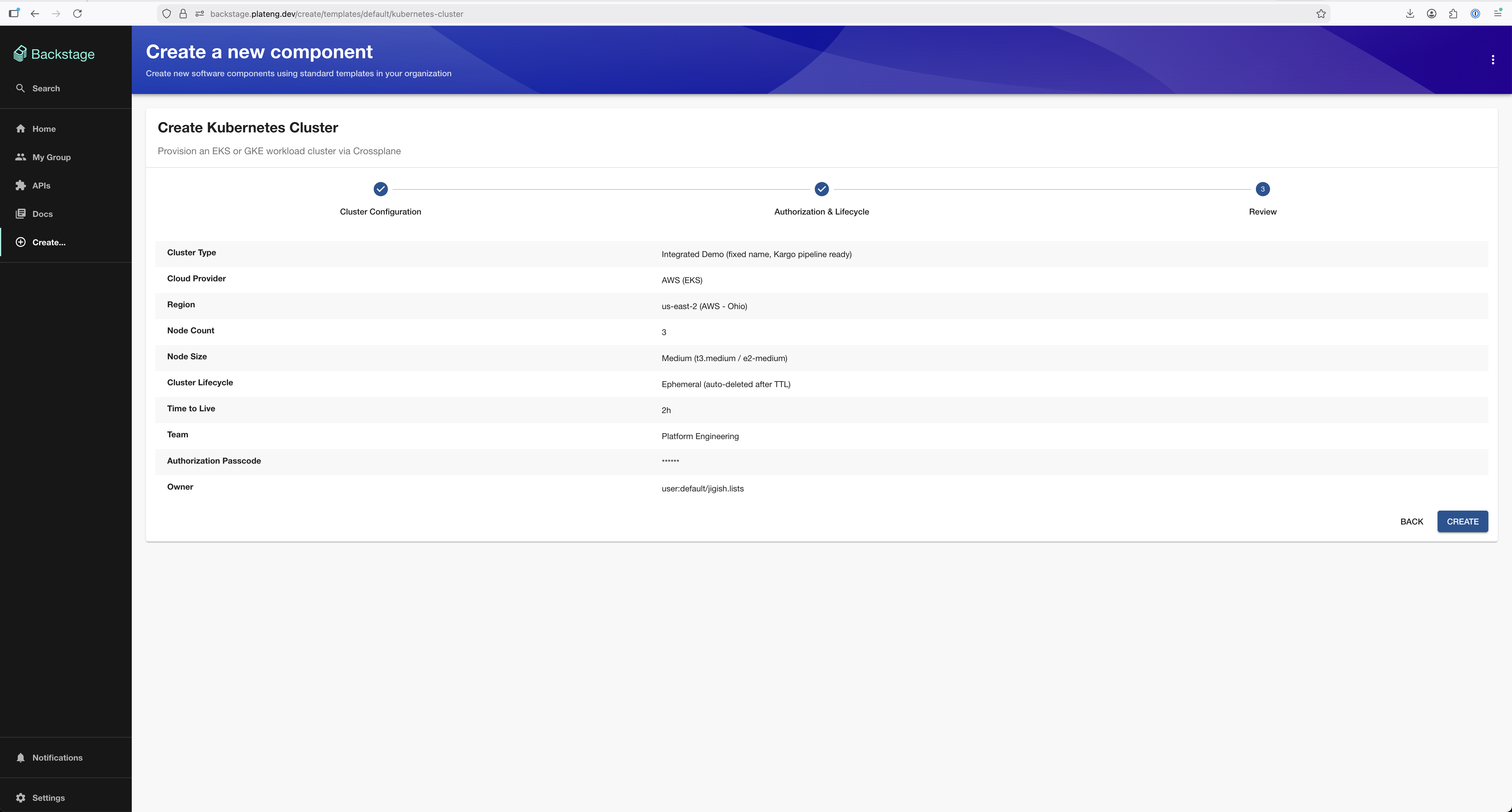
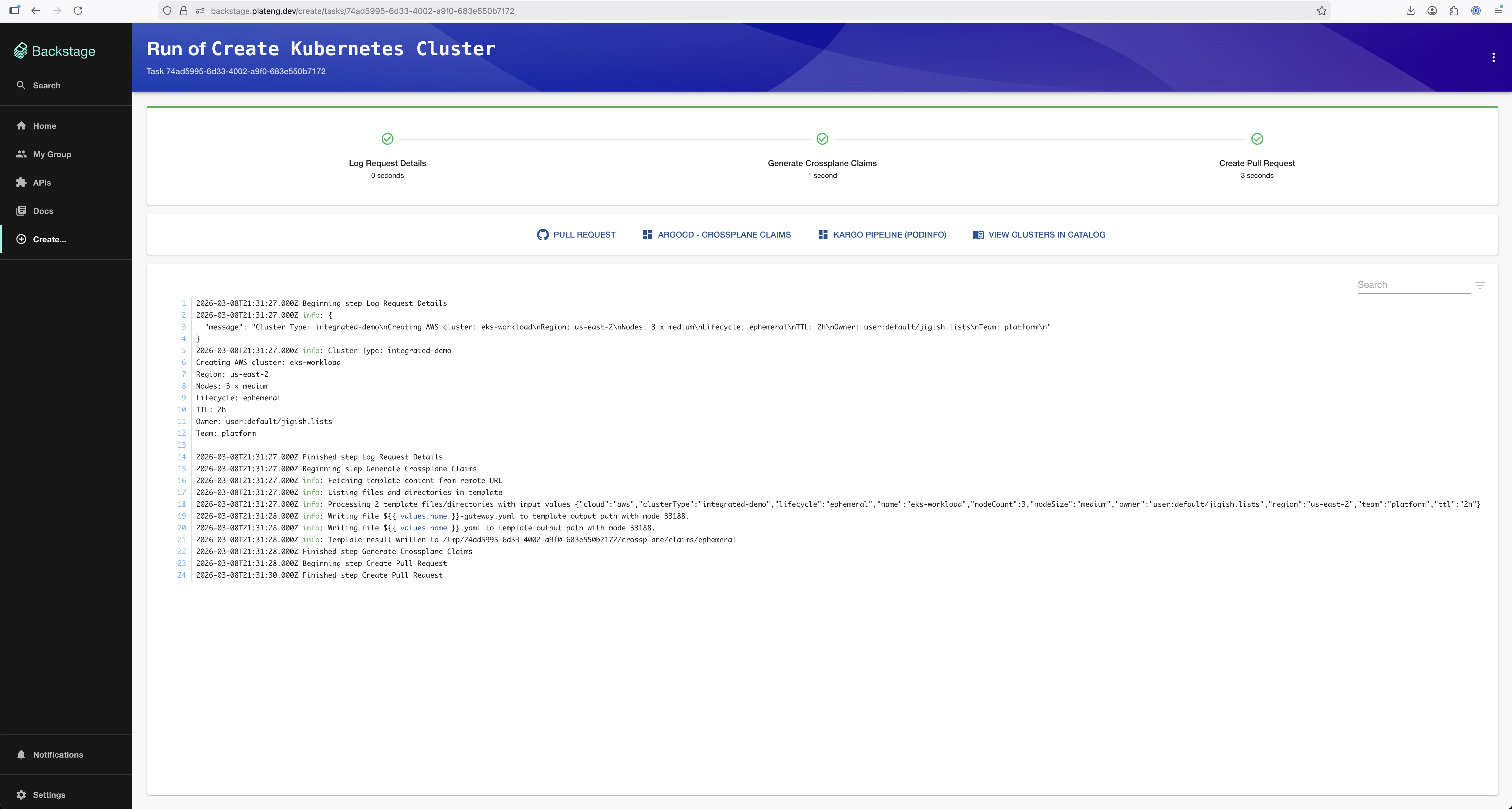
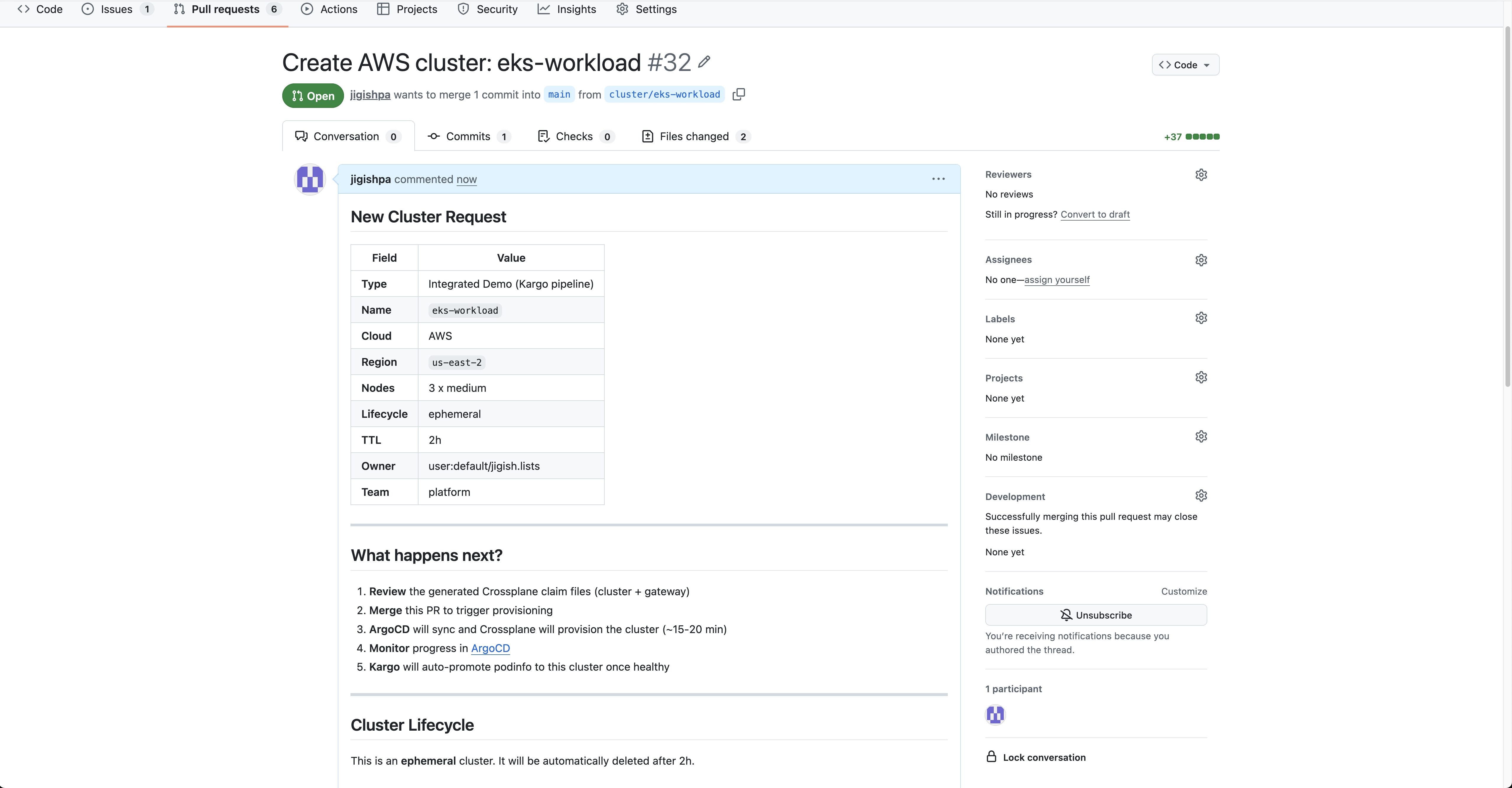
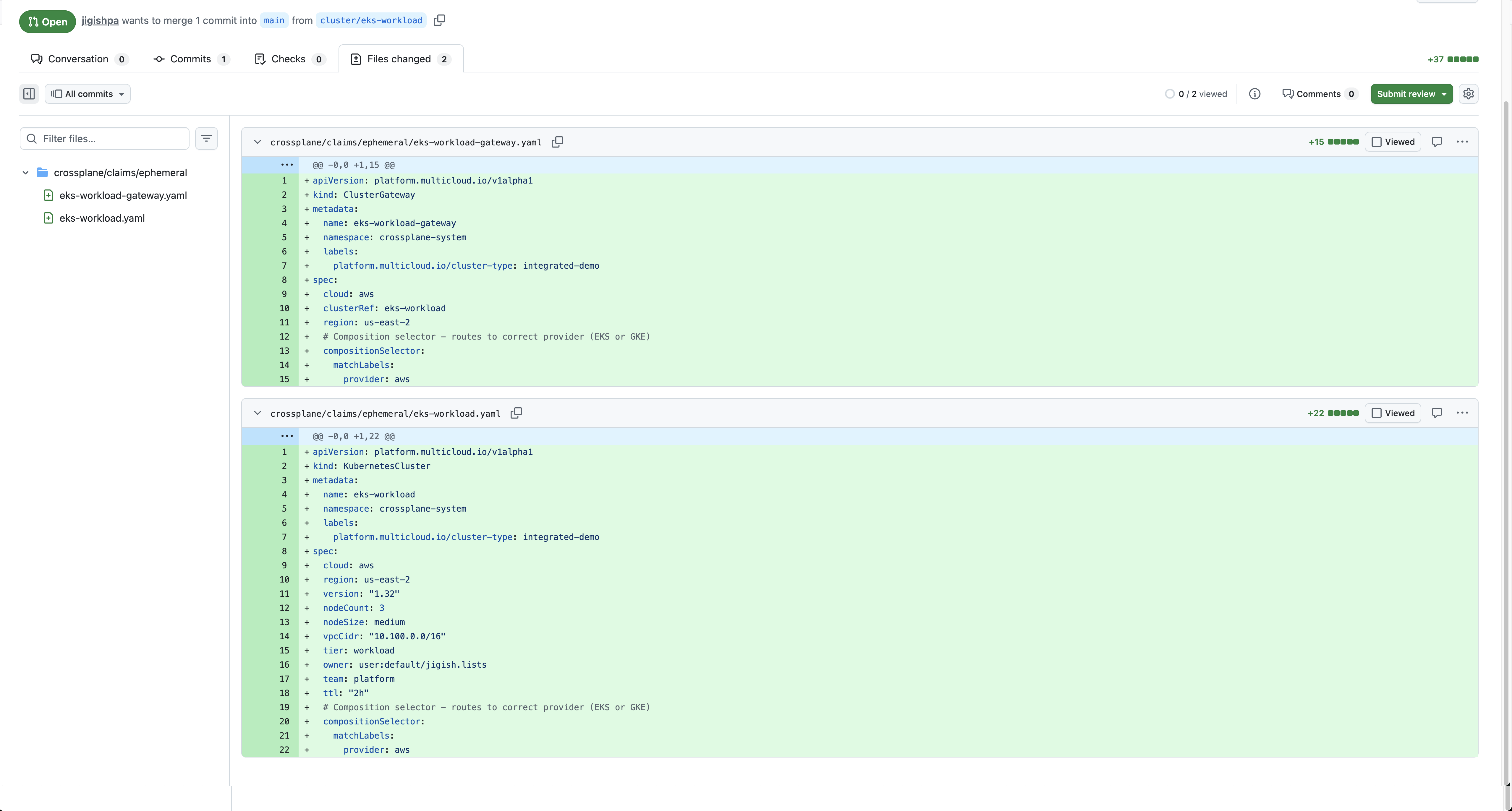
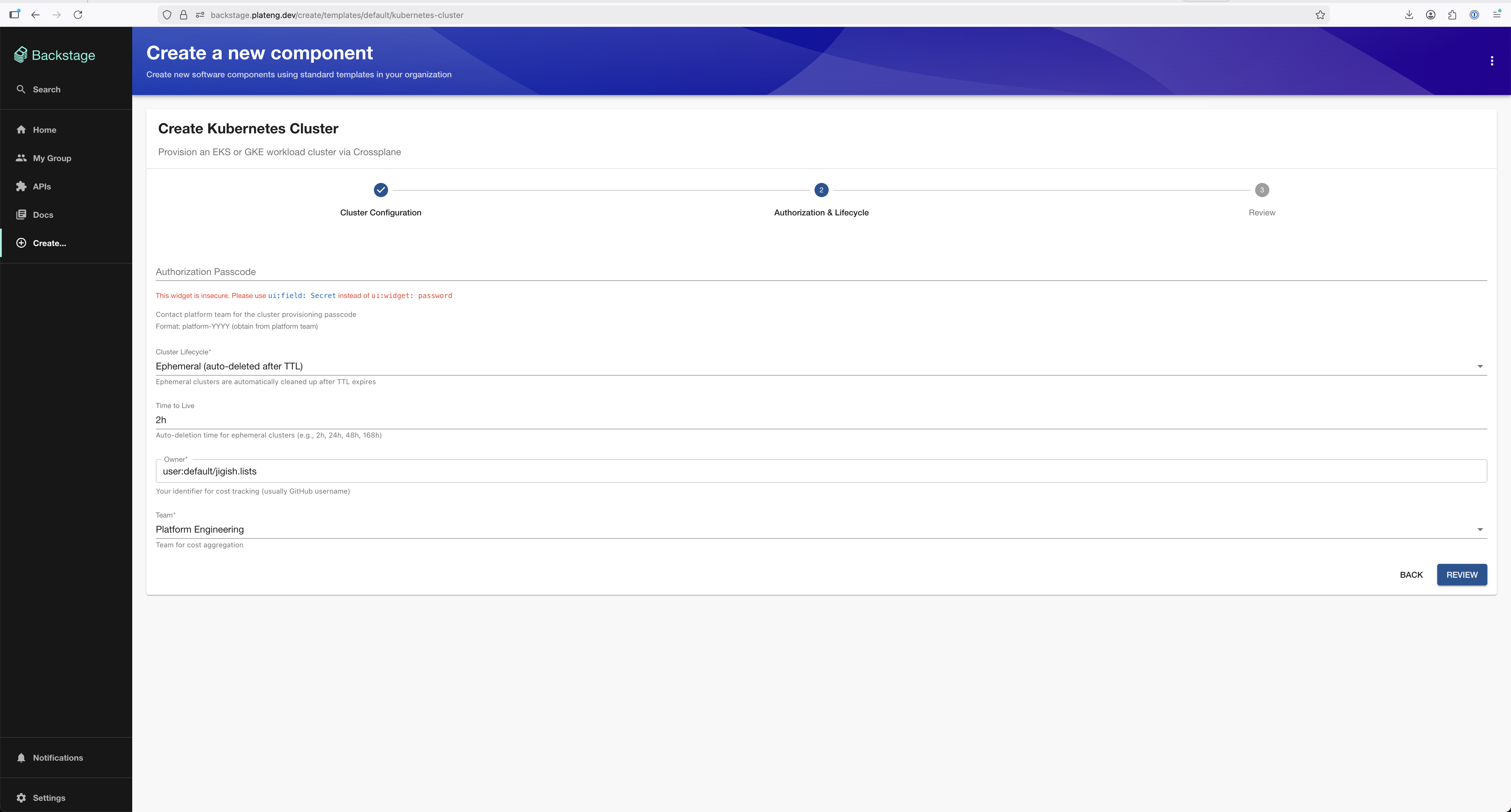
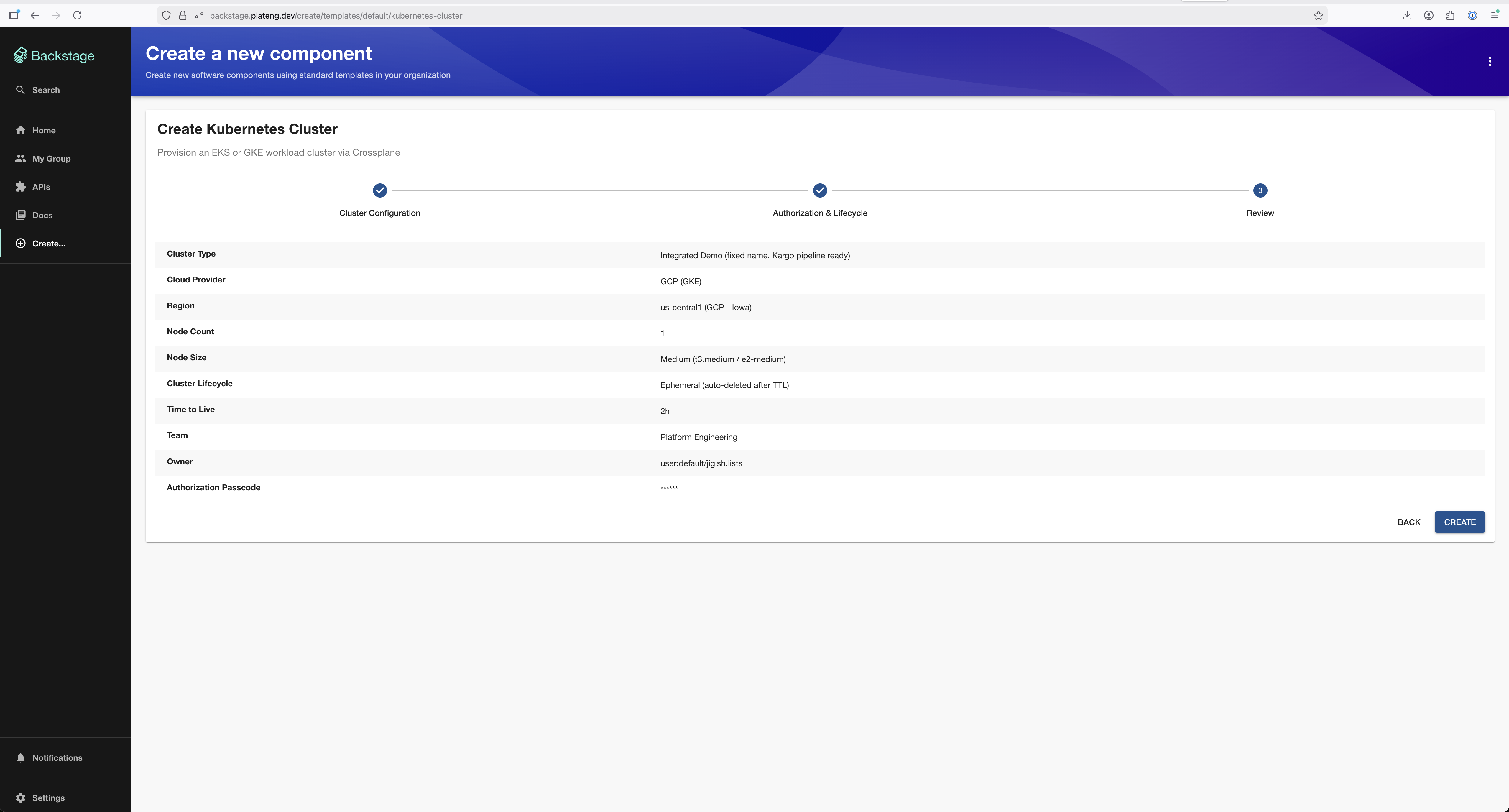
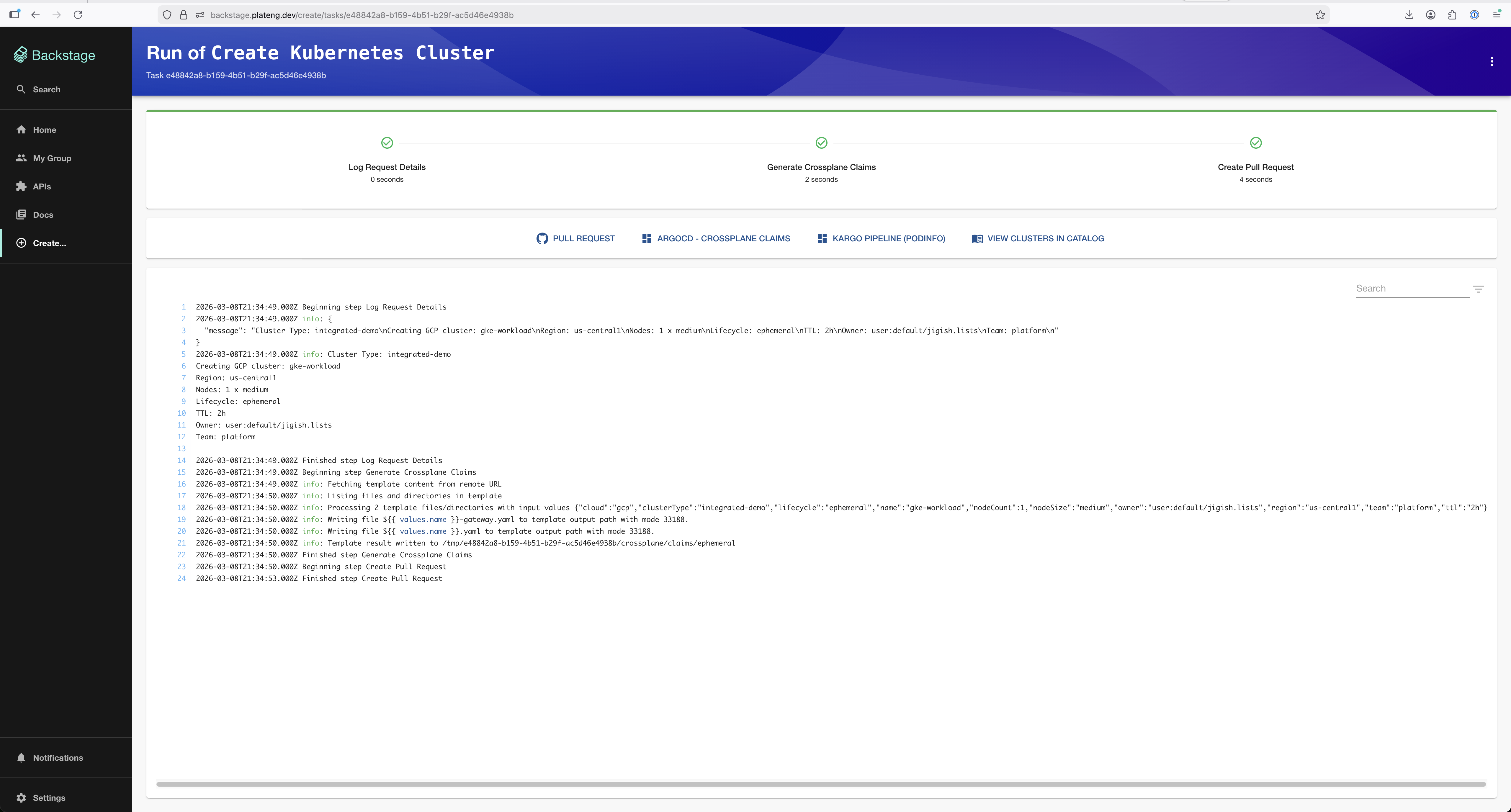
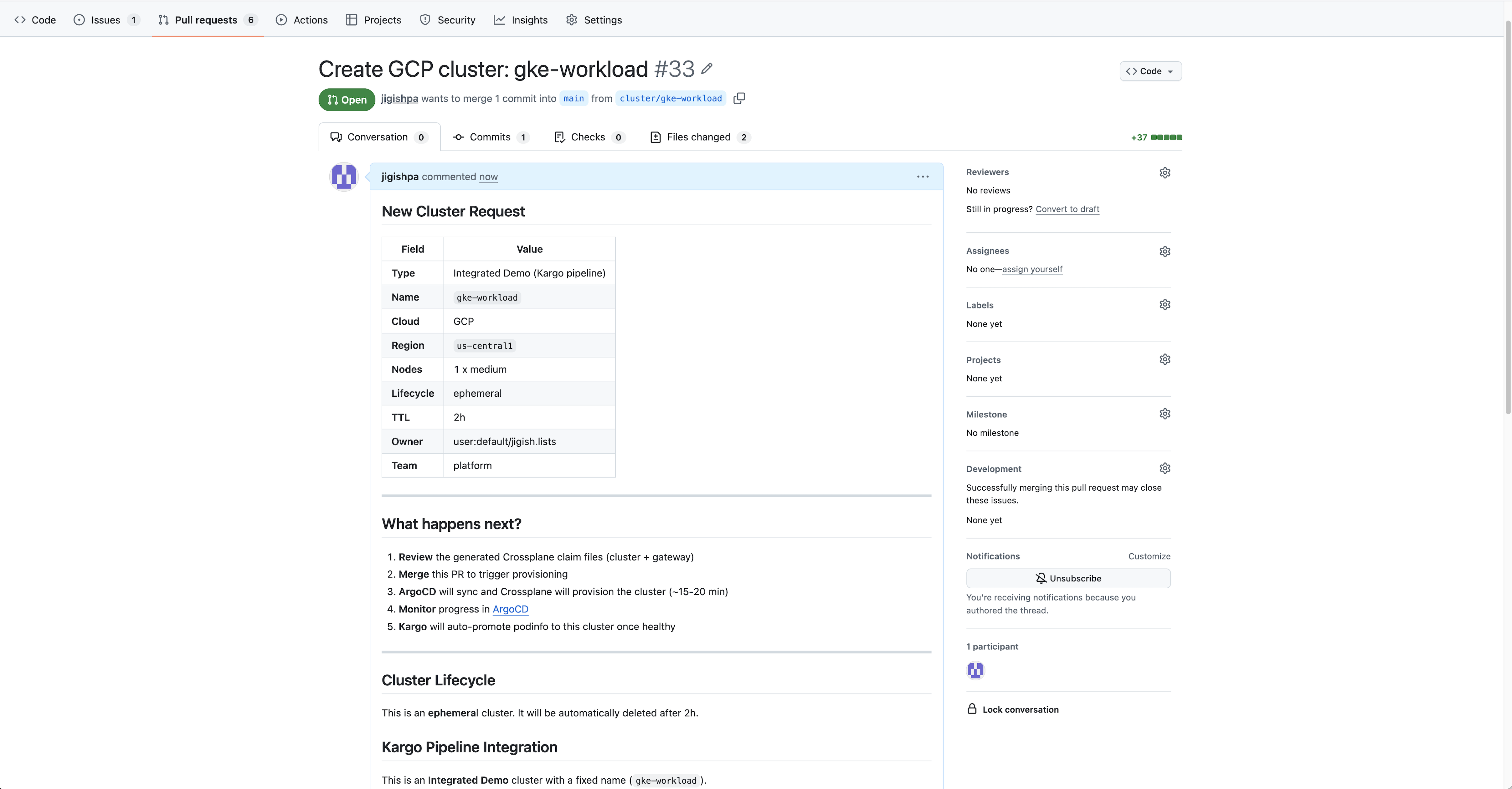
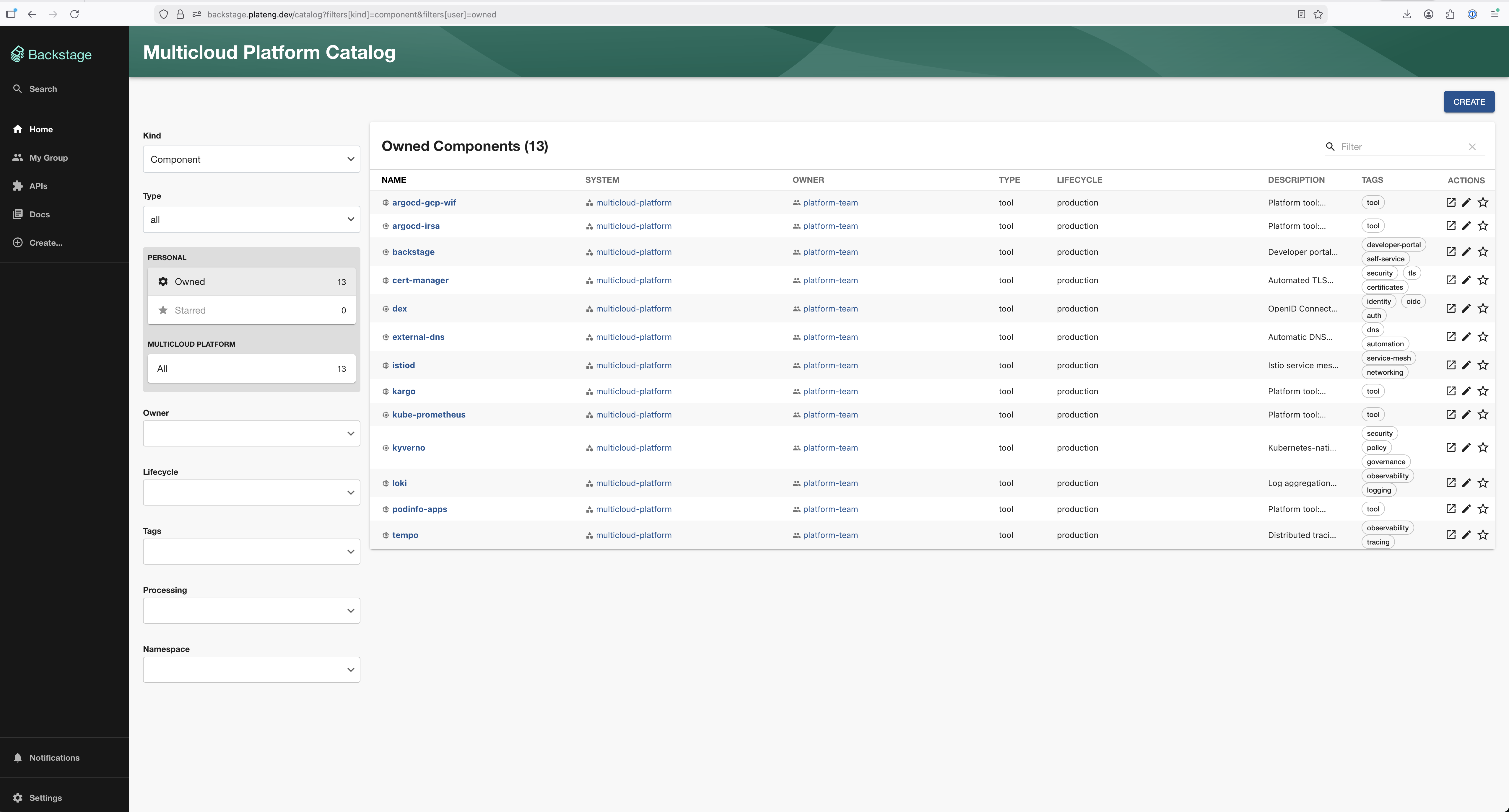
Self-Service Cluster Creation
Developers provision EKS or GKE clusters through a Backstage template. The template generates Crossplane claims, opens a GitHub PR, and once merged, ArgoCD + Crossplane provision the cluster automatically.